Quantum-Computer Resistant Cryptocurrencies
In simpler terms, encryption, which is the encoding of information, data and messages in a way that only the authorized party will read it, refers to using some algorithm to generate some random key (pseudo-random encryption) and a text that can only be read if decrypted with the previously generated key.
In principle, however, it is possible to decrypt encrypted data, messages, and information without the key, but if the encryption scheme was very well crafted, decryption would take massive computational resources, advanced skills than an ordinary person would afford, and several years.
With current technologies, RSA and ECC-based data protection systems would take a hundred years to break into. RSA cryptosystem is an encryption scheme that derives its security from the difficulty involved in factorizing integers. For instance, even factorizing numbers with a few hundred digits take a hassle. So with the current methods, it would take many years to break into RSA-protected data.
Cryptocurrencies use public and private keys where the user has to have a private key that he or she should use in order to spend or transact cryptocurrencies.
We are now using computers that can factorize very large numbers and do millions of calculations or iterations in a second! Great! But enter the quantum computer -- the computer of tomorrow -- that will be able to factorize large numbers exponentially or polynomial manner such that it can perform billions of calculations and solve billions of problems exponentially faster than today's most advanced computers!
The idea was theorized by Nobel prize-winning physicist Richard Feynman in 1982. The interest in the machines boomed following Peter Shor's devising of a quantum computer algorithm in 1994, but there are other algorithms such as the much faster Simon's algorithm.
Modern computers are limited to processing either a 1 or 0 bit at a single unit time, but the quantum is based on qubits, each of which can assume the state of 0, 1, or a superposition of the two at a unit time. It means they will be capable of doing many calculations simultaneously.
Quantum computers will pose a new threat to modern RSA and ECC-based data protection methods and cryptocurrencies as a whole: they can break the cryptography and encryption within days if not hours, given the higher processing power and speed. They will be able to do so because they can factorize these large numbers far more quickly than the best available methods today, using polynomial-time algorithms for prime factorization, according to research.
Quantum computers will, therefore, be able to override security barriers including breaking much of the public key cryptography used to protect data, information and communications today. It simply means that new solutions will be needed to protect cryptocurrencies.
Do we have quantum computers yet? When do we expect the threat?
In the last few years, Google, Intel and IBM either already have these computers or have invested into research on quantum computing.
Google has been vocal about its 1,000-qubit quantum computer it shares with NASA and Universities Space Research Association, a D-Wave 2X quantum computing machine that can figure out algorithms at 100,000,000 times the speed that a traditional computer chip.It operates at 15 millikelvin (very, very, very cold). It is installed at the Quantum Artificial Intelligence Lab.
Google is using it in various applications including machine learning, speech recognition, robotic missions into space, air-traffic management, and web search. It claims the machine is 100 million times faster than an ordinary laptop.
For now, however, modern quantum computers would safely be regarded as very slow, and can do no better than calculate the prime factors of 21. For large-scale applications thought for a quantum computer, some say it should have about 10 billion quantum bits or qubits.
There is no doubt that the challenge of building a quantum computer that can factorize very large numbers is remain enormous—but not insurmountable. Qubits are first encoded then manipulated with dangerous methods and processes such as laser beams, microwaves, electric fields or other probe. There will also be decoherence errors to deal with when building a real quantum computer of a huge processing magnitude. That's to mention just a few complexities.
It means it will take more time to produce quantum computers that can factorize very huge numbers. How long is what people aren't sure but activity will certainly increase within the next 10 to 20 years.
However, the threats are real. Ion Quantum Technology Group at Sussex University in the UK revealed in February, the first ever open-source blueprint for a practical quantum computer
The National Security Agency noted on its website on August 11 that it would shift encryption of government and military data away from the current cryptographic schemes to new ones yet to be determined, that can resist attack by quantum computers.
Quantum-computer insecure encryption explained
The RSA, the Diffie-Hellman key exchange, and the elliptic curve cryptography are not quantum computer safe.
In RSA, a message is encrypted using the intended recipient's public key that is then decrypted with a private key. The difficulty of the private key computation is related to the hardness of prime factorization.
In Diffie-Hellman method, two parties establish a shared secret key over an insecure network and this they use for encrypted communication. The hardness of the discrete logarithm problem determines the security of the secret key.
The elliptical method relies on the mathematical properties of elliptic curves to generate public and private keys. The hardness of the elliptic-curve discrete logarithm problem is connected to the difficulty of recovering the private key.
How can we protect today's crypto tomorrow?
Researchers believe that if it is possible to build a quantum computer, then it is possible to build what can protect data against it. A number of suggestions have been fronted as we shall see below.
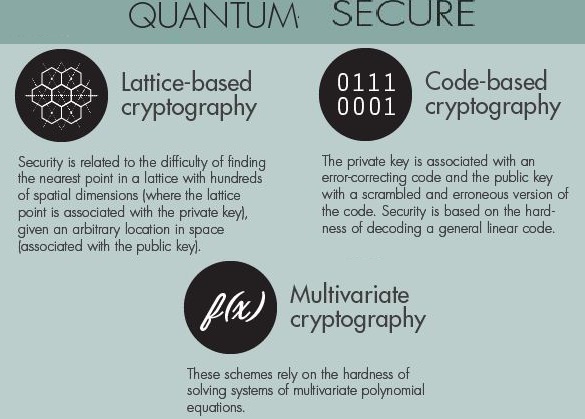
Three quantum-secure methods have been proposed and work is still going on: We have lattice-based cryptography, code-based cryptography, multivariate cryptography.
In a lattice-based cryptography scheme, the private key is associated with the lattice point while the public key is associated with the arbitrary location in space. It relies on how easy it is to get lost in a 500-dimensional lattice: it can be difficult to find the next lattice point given an arbitrary location in 500-dimensional space.
Code-based cryptography method is also code error adding and correcting method and involves use as a ciphertext a word of a carefully chosen linear error-correcting code—a binary Goppa code into which random errors have been added. This would form the public key. Legitimate users who know the a secret trapdoor decoding algorithm for the code can remove the errors and recover the cleartext.
In multivariate cryptography, the encryption and decryption algorithms are based on multivariate mappings and the security of the private key depends on how difficult it is to solve a a system of a parametric simultaneous multivariate equations involving polynomial or exponential mappings.
Quantum-safe cryptocurrencies
Cryptocurrencies currently largely rely on the public and private key system. To spend the coins, a user will need to posses and use a private key to unlock them. If someone learns of that private key before the legitimate user, then they would spend those coins instead. That threat is real in all realism possibilities of the quantum computers for all currencies that utilize elliptic curve cryptography and other forms of cryptography that is vulnerable to quantum computers, because the quantum computers would calculate the private key from the public key in a matter of minutes.
Systems like Ethereum currently use elliptic curve cryptography that aren't quantum-safe. Bitcoin uses two hashing functions -- SHA-256 and RIPEMD-160 and Elliptic Curve DSA.
Last year, a team of scientists warned that quantum computers would render Bitcoin insecure because they could calculate the private from the public one in a few minutes. But a lot has been going on in terms of securing cryptocurrencies against quantum computers.
Dr. Peter Waterland has developed the Quantum Resistant Ledger (QRL), which is a public blockchain ledger that uses post-quantum secure signature scheme known as the Extended Merkle Signature Scheme called XMSS to secure blockchains. QRL uses a Proof of Stake algorithm that uses hash-chains and hash-based pseudo random number functions and does not rely on conventional signatures.
List of Quantum Resistant Cryptocurrencies
QRL - Quantum Resistant Ledger
QRL is currently an ERC20 token that trades on the major exchanges, including Bittrex, Tidex and Liqui.io.
The technology will help secure transactions but will also employ . Other nodes can dial up this key and create secure decentralized communication channels for the messaging system.
The company plans to using the innovation in helping to secure company communications and other services in addition to being a cryptocurrency vault.
Russian Quantum Center
May this year, The Russian Quantum Center claimed to have made the first quantum secure blockchain that makes the blockchain completely "un-hackable" even with a quantum computer. It combines quantum key distribution (QKD) with post-quantum cryptography. The blocks would be signed by quantum keys rather than the traditional digital signatures and the quantum keys would be generated by a QKD network. The center said it had tested this technology in one bank.
IOTA and The Tangle
IOTA calls itself the next generation blockchain because it relies on Internet of Things technology. It uses the Winternitz One-Time Signature Scheme for hash functions, and this system is said to be more quantum secure than one used in Bitcoin.
Winternitz One-Time Signature (OTS) scheme employs the Lamport signatures claimed to be resistant to quantum computer algorithms if they have large hash functions. With IOTA's wallet, you cannot reuse an address to sent or receive a transaction because reusing a private key in a Lamport scheme halves the security level of the signature.
The security is achieved because the number of nonces one needs to check to find a suitable hash for issuing a transaction is only 38 when the gain of efficiency for an ideal quantum computer would be 34 to 81 according to Dr. Sergui Popov comparing IOTA with Bitcoin to explain quantum resistance.
Also, the time to find a nonce in this IOTA's algorithm is also not much larger than time needed for other tasks necessary to issue a transaction.
Ethereum?
Last year, Ethereum did say that they could switch to a different quantum computer safe cryptography.
Ethereum has also recently said that it would allow users to choose planned quantum computer safe addresses. Ethereum will use the proposed EIP 86 and Casper to support any digital signature algorithm. This way it will supports signature mixers and custom cryptography such that users can upgrade to ed25519 signatures, Lamport hash ladder signatures or whatever other scheme they want on their own terms, without sticking with ECDSA.
However, mixing addresses could produce the potential for retroactive decryption and infiltration.